Innovation Insights: Our Security Fabric Vision is Reality
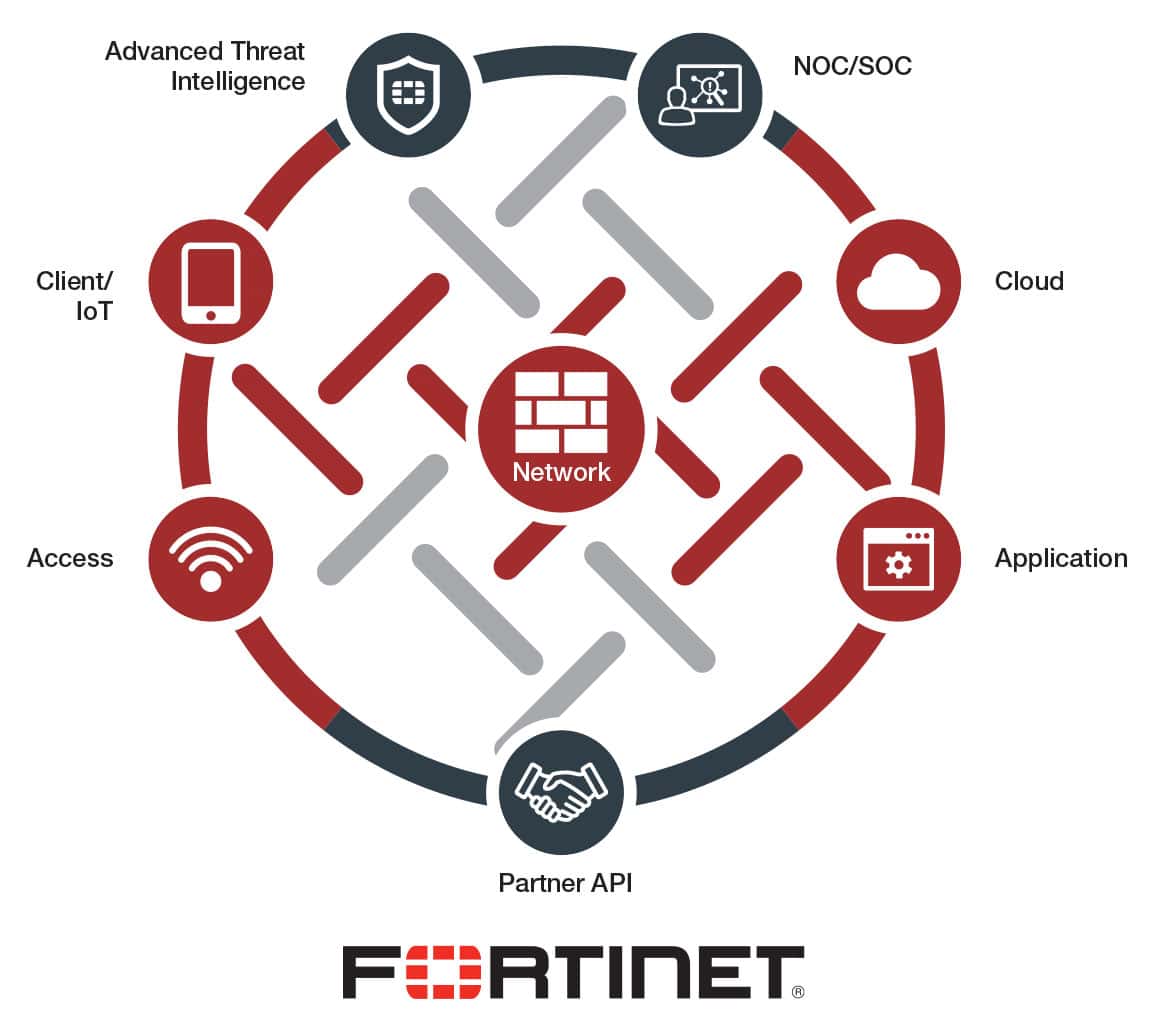 Nearly two years ago, Fortinet unveiled their technology vision of the Fortinet Security Fabric. With the release of FortiOS 6.0, they have turned that vision into a full-fledged reality with a truly integrated and automated security framework designed for today’s dynamic networks. FortiOS is already the world’s most deployed network security operating system, and this latest release delivers more than 200 new features and capabilities designed to strengthen and expand the power of the Security Fabric through broad visibility, integrated detection of advanced threats, and automated response, combined with the continuous trust assessment required to secure today’s digital business.
Nearly two years ago, Fortinet unveiled their technology vision of the Fortinet Security Fabric. With the release of FortiOS 6.0, they have turned that vision into a full-fledged reality with a truly integrated and automated security framework designed for today’s dynamic networks. FortiOS is already the world’s most deployed network security operating system, and this latest release delivers more than 200 new features and capabilities designed to strengthen and expand the power of the Security Fabric through broad visibility, integrated detection of advanced threats, and automated response, combined with the continuous trust assessment required to secure today’s digital business.
Features in FortiOS 6.0 include:
- Enhanced secure SD-WAN functionality, threat detection services, and expandedvisibility from IoT to multi-cloud networks protects the vast attack surface being created by digital transformation strategies.
- Expanded Cloud Connectors within the Security Fabric now include visibility of private, public, and SaaS clouds, including Connectors for VMware NSX, Cisco ACI, Nokia Nuage, AWS, Azure, Google Cloud, Oracle Cloud, Dropbox, Box, Salesforce, and more.
- New automated workflows, integrated audit and compliance services, and customized ranking and industry benchmarking deliver the next level of cybersecurity management and control.
- Business, network, and entity-level tagging functionality enable precise business segmentation, providing the critical building blocks necessary for intent-based network security.
- Other features include new traffic shaping capabilities to guarantee bandwidth for critical applications, zero-touch deployment for plug-and-play SD-WAN location management, and one-touch VPN to leverage common cloud VPN access.
The Challenge of Legacy Security Solutions
Today’s network evolution is doing more than simply expanding the network footprint. New applications, elastic infrastructures, multi-cloud environments, and IoT devices have pushed the performance capabilities of today’s security technologies to their limit. Traditionally, enterprises have accepted these limitations by being willing to trade some network performance for security. But in today’s digital economy, where success is often measured in microseconds, this is a compromise that organizations can no longer afford to make.
In addition to performance and volume, the other major challenge facing legacy security deployments is the growing complexity of today’s networks. The more complex a network, the harder it is to secure, and today’s networks are being built around hyperconnecting data, devices, and applications. And therein lies the problem with attempting to apply a traditional security strategy: while individual products and platforms may work to specifications and expectations, they also operate individually, isolated from other security solutions. While there may be some degree of connectivity between similar devices, there is ultimately no real continuity between security islands. Which means that security managers are not only unable to see across the entire network, they can’t track data across resources that are in constant flux.
In such an environment, device isolation significantly complicates the management and implementation of consistent security protocols and policies. It also contributes to a lack of consistency in the threat intelligence available to different security devices, which means that threats, especially the more sophisticated ones, can be easily missed.
A Security Rethink with a New Approach
What this means is that as the speed and scale of networks and cyber threats expands, security must undergo a parallel transformation if it intends to protect today’s digital businesses. That requires integrating security into all areas of digital technology, with the end goal of dynamically translating user intent into automated security that can see, respond to, and even anticipate cyber events.
Unlike silo security approaches, FortiOS 6.0 delivers advanced security innovation through hundreds of new features and capabilities designed to tightly integrate security solutions into a single proactive and consistent system distributed seamlessly across the network. This includes broad protection and visibility across the expanding attack surface; the orchestration of segmentation from the branch and endpoint into the core, through the data center, and out to multi-cloud environments; the ability to automatically marshal advanced threat protection resources to combat threats detected anywhere across the network; and continuous security assessments and audits that provide ongoing improvement to the entire network’s security posture.
The Fortinet Security Fabric achieves this by leveraging open standards and a common operating system that allow different security technologies to operate as a single, consistent system. This holistic approach, now fully realised in FortiOS 6.0, enables consistent visibility and integrated control that can dynamically span and adapt to the elastic networks that organisations are deploying today.